Docker containers can quickly accumulate during development, testing, or CI/CD workflows, leading to unnecessary disk usage and clutter. Knowing how to safely identify and remove unused containers helps maintain a clean and efficient environment. In this guide, you will learn practical and safe methods to clean up Docker containers without affecting active workloads.
Quick cheat sheet for Docker container cleanup
| Task | Command |
|---|---|
| List running containers | docker ps |
| List all containers | docker ps -a |
| List only exited containers | docker ps -a -f "status=exited" |
| Remove specific container | docker rm <container_id> |
| Force remove running container | docker rm -f <container_id> |
| Remove all stopped containers | docker container prune |
| Remove containers older than 24h | docker container prune --filter "until=24h" |
| Remove exited containers (one-liner) | docker rm $(docker ps -a -q -f "status=exited") |
| Auto remove container on exit | docker run --rm <image> |
- Use
docker rm→ when you want full control - Use
docker container prune→ when you want fast cleanup - Use
--rmflag → to avoid cleanup altogether - Use filters → for safe and targeted removal
Identify unused Docker containers effectively
List only stopped containers (exited state)
The most common way to identify unused containers is by listing those in an exited state, as they are no longer running and often safe to remove. You can also list all containers using docker ps -a to get complete visibility:
docker ps -a -f "status=exited"This helps quickly filter out containers that are no longer in use and likely candidates for cleanup.
Find containers based on age (inactive for X days)
You can identify exited containers older than a specific date using:
docker ps -a --filter "status=exited" --format '{{.ID}} {{.Names}} {{.CreatedAt}}' | awk '$3 < "2026-03-29"'Example output:
81d0a004bfa4 pingman 2026-03-18 07:41:56 +0000 UTCThis command works as follows:
- Lists only stopped containers
- Prints container ID, name, and creation timestamp
- Filters containers created before the given date (
YYYY-MM-DDformat works with string comparison)
For better readability, you can also use a table format:
docker ps -a --filter "status=exited" --format 'table {{.ID}}\t{{.Names}}\t{{.Status}}\t{{.CreatedAt}}' | awk 'NR==1 || $4 < "2026-03-29"'In real-world scenarios, filtering by creation date is helpful but not always accurate because a container might be created long ago but stopped recently. For precise control, use docker inspect to check when the container actually stopped:
docker inspect --format '{{.ID}} {{.Name}} {{.State.FinishedAt}}' <container_id>You can combine this with scripting to compare timestamps and remove only containers inactive for a certain number of days.
Inspect container usage before deletion
Before removing a container, especially in production, it is important to verify its usage history:
docker inspect --format='{{.State.Status}} {{.State.FinishedAt}}' <container_id>Safe removal strategies (production vs development)
Remove specific containers safely
For precise and controlled cleanup, remove containers individually:
docker rm <container_id>This method is recommended in production because it minimizes the risk of accidentally deleting important containers. If required, you can restart containers instead of removing them using docker restart container:
Bulk cleanup using docker container prune
To quickly remove all stopped containers:
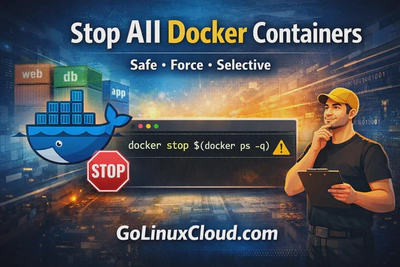
docker container pruneThis is useful in development environments where containers are frequently created and discarded. In some cases, you may want to stop all running containers first using docker stop all containers before cleanup:
Filter-based cleanup for controlled deletion
For safer bulk operations, combine filters to target only specific containers:
docker container prune --filter "until=24h"Or:
docker rm $(docker ps -a -q -f "status=exited")This approach gives more control compared to blind cleanup and is suitable for semi-production environments.
docker rm vs docker container prune vs --rm flag
Key differences and use cases
| Method | Control Level | Use case |
|---|---|---|
| docker rm | High | Remove specific containers manually |
| docker container prune | Low | Remove all stopped containers quickly |
| docker run --rm | Very High | Prevent unused containers from being created |
- Use
docker rmwhen you want full control - Use
docker container prunewhen you want quick cleanup - Use
--rmwhen you want to avoid cleanup completely
When NOT to use prune in production
Avoid using docker container prune in production environments when:
- Containers may still be needed for debugging
- Logs or state information are required
- Multiple teams are sharing the same host
- You are unsure about container dependencies
In such cases, always prefer manual removal or filtered cleanup to prevent accidental data loss or service disruption.
Automate Docker cleanup (best practices)
Cron-based cleanup strategy
For environments where containers are created frequently (CI/CD, testing), automating cleanup using cron ensures your system remains clean without manual intervention. You can also optimize builds to reduce unused containers using docker build no cache:
Example cron job (runs daily at midnight):
0 0 * * * docker container prune -fFor safer cleanup, combine with filters:
0 0 * * * docker container prune --filter "until=24h" -fThis avoids deleting recently stopped containers.
Script-based cleanup with conditions
For better control, use a script that removes containers only if they meet specific criteria such as age or status.
Example:
#!/bin/bash
threshold_days=7
current_time=$(date +%s)
docker ps -a --filter "status=exited" --format '{{.ID}}' | while read id
do
finished=$(docker inspect --format '{{.State.FinishedAt}}' $id)
finished_at=$(date -d "$finished" +%s 2>/dev/null)
if [ ! -z "$finished_at" ]; then
diff_days=$(( (current_time - finished_at) / 86400 ))
if [ $diff_days -gt $threshold_days ]; then
echo "Removing container $id (inactive for $diff_days days)"
docker rm $id
fi
fi
doneThis ensures only containers inactive for a defined period are removed.
Avoid accidental deletion using labels
In production, use labels to protect important containers from cleanup:
docker run -d --label keep=true nginxThen exclude them during cleanup:
docker ps -a --filter "label!=keep=true"Or in scripts:
docker rm $(docker ps -a -q --filter "status=exited" --filter "label!=keep=true")This helps prevent accidental deletion of critical containers.
Common mistakes while removing containers
Removing running containers without validation
Using force removal:
docker rm -f <container_id>can terminate active workloads and cause service disruption.
Always verify container status before removal:
docker psLosing important data due to volumes
Containers may be stopped but still linked to volumes storing critical data.
Before removing containers, check volume usage:
docker inspect <container_id>Avoid removing containers blindly if they are associated with persistent storage.
Overusing prune command blindly
Running:
docker container prunewithout filters removes all stopped containers, regardless of importance.
This can lead to:
- Loss of debugging data
- Accidental removal of reusable containers
Always use filters or manual checks in production.
Frequently Asked Questions
1. How do I remove unused Docker containers safely?
You can remove unused Docker containers safely using docker rm for specific containers or docker container prune for bulk cleanup, ensuring containers are not actively in use.2. What is the difference between docker rm and docker container prune?
docker rm removes specific containers manually, while docker container prune removes all stopped containers at once, making it faster but less controlled.3. Can I automatically remove Docker containers after execution?
Yes, you can use the--rm flag with docker run to automatically remove containers once they stop, preventing accumulation of unused containers.4. Is docker container prune safe in production?
It should be used with caution in production, as it removes all stopped containers without checking their importance or recent usage.Summary and Best Practices
- Use
docker rmfor safe and controlled removal - Use
docker container prunefor quick cleanup in development - Use filters and scripts for controlled automation
- Use labels to protect critical containers
- Prefer automation with conditions over blind cleanup
A balanced approach ensures efficient resource usage without risking data loss or service disruption. For a complete understanding of container lifecycle, refer to manage docker container with examples.




![Optimize Golang Docker images [Multi-Stage Build]](/golang-docker-multi-stage-build/golang-docker-multi-stage-builds_hu_f3e502624a858ad6.webp)

![COMPLETELY Uninstall Docker in Ubuntu [100% Working]](/ubuntu-uninstall-docker/uninstall-docker_hu_b078fa929efc80f7.webp)